Google Voice is a cloud-based phone service developed by Google that provides users with a virtual phone number for calls, SMS, and voicemail management across multiple devices. Unlike a traditional carrier number, a Google Voice number operates entirely through your Google Account, which means your account credentials are the single point of access for your entire communication history.
This architecture creates a unique security challenge. A compromised Google Account does not just expose your email or documents, it exposes every call log, voicemail transcript, SMS conversation, and linked forwarding number stored under that account. For individuals, this means personal communication data is at risk. For businesses and marketers managing multiple numbers, a single account breach can disrupt entire operational workflows.
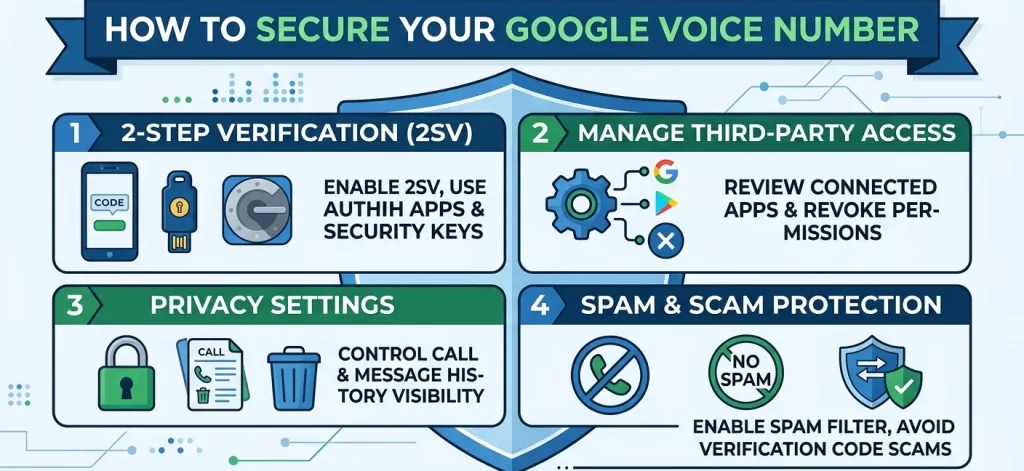
Google Voice account number security requires a layered approach combining two-step verification, third-party access management, privacy settings, spam filters, and data encryption to protect your number, call history, and messaging data from unauthorized access.
This guide covers each layer in detail, from enabling the strongest available verification method to understanding exactly how Google stores and encrypts your Voice data, so you can build a security configuration that matches your actual usage needs.
Table of Contents
ToggleSecuring Your Google Voice Account With 2-Step Verification
Two-step verification (2SV) is the single most effective security measure for protecting a Google Voice account from unauthorized login attempts.
How to Enable 2-Step Verification on Google Voice
Google Voice security is managed through your primary Google Account settings. To activate 2SV:
- Go to myaccount.google.com
- Select Security from the left panel
- Under “How you sign in to Google,” click 2-Step Verification
- Follow the on-screen prompts to add your verification method
Once enabled, every new login attempt requires both your password and a secondary verification code blocking unauthorized access even if your password is compromised.
Recommended Verification Methods
Authenticator App (Strongest)
Google Authenticator or Authy generates time-based one-time passwords (TOTP) that expire every 30 seconds. This method works offline and is not vulnerable to SIM-swapping attacks.
Hardware Security Key
A physical FIDO2-compatible key (such as YubiKey) is the highest-security option. It requires physical possession of the device making remote account takeovers virtually impossible.
SMS Verification Code (Basic)
While convenient, SMS-based verification is the weakest option due to SIM-swap vulnerability. Use it only as a backup method, not as your primary 2SV layer.
Managing Third-Party Access to Your Google Voice Account
Third-party apps and services connected to your Google Account can access Google Voice data if granted permission. Unreviewed access is a common but overlooked security risk.
How to Review Connected Apps and Permissions
Audit Your Connected Applications
Navigate to myaccount.google.com/permissions to see every third-party app with access to your Google Account. Remove any applications you do not recognize or no longer use actively.
Understand Permission Scopes
Each connected app requests specific permission scopes. An app with “read and manage your Google Voice account” scope can access your call logs, messages, and account settings. Restrict permissions to only what each app genuinely requires.
Revoke Unused OAuth Tokens
OAuth tokens granted to older applications remain active indefinitely unless manually revoked. Audit and revoke unused tokens quarterly to minimize your account’s attack surface.
API Access and Developer Integrations
If you use Google Voice through third-party CRMs, auto-dialers, or communication platforms, ensure those integrations use OAuth 2.0 authentication not stored plaintext credentials. Services that require your Google password directly should never be granted access.
Privacy Settings for Call and Messaging History
Google Voice stores your call history, voicemail transcripts, and SMS message history by default. Managing these settings reduces your data exposure across Google’s infrastructure.
Controlling Call History Visibility
Disable Call History Storage
In Google Voice settings, navigate to Calls and disable “Show my Google Voice calls in Google activity.” This prevents call data from appearing in your broader Google Account activity log.
Delete Individual Records
You can delete specific calls, messages, or voicemails directly from the Google Voice app or web interface. Select the conversation and choose Delete to remove it from your account permanently.
Managing Voicemail Transcription Data
Voicemail Transcript Storage
Google Voice automatically transcribes voicemails using speech recognition. These transcripts are stored in your account and indexed within your Google activity. If transcript privacy is a concern, delete voicemails after listening or disable transcription in Settings → Voicemail.
Google Activity Controls
Visit myaccount.google.com/activitycontrols to manage how Google stores your Voice activity. You can pause storage or enable auto-delete at 3-month or 18-month intervals.
Protecting Against Spam and Scams on Google Voice
Spam calls and phishing attempts targeting Google Voice numbers have increased significantly. Built-in filters and behavioral settings reduce exposure substantially.
Enabling Spam Call Filtering
Google Voice Spam Filter
In Google Voice settings under Calls, enable Filter spam calls. Google’s spam detection algorithm flags known spam numbers and sends them directly to voicemail without ringing your device.
Do Not Disturb Mode
For periods requiring complete call silence, enable Do Not Disturb in Google Voice settings. All incoming calls go to voicemail and no notifications are triggered.
Recognizing and Avoiding Google Voice Scams
Number Porting Scams
A common scam involves tricking account holders into sharing their Google Voice verification code, which attackers use to port the number to their own account. Google will never ask you to share a verification code via phone or text. Treat any such request as a phishing attempt.
Spoofed Caller ID Attacks
Attackers spoof legitimate numbers to appear as Google support or trusted contacts. Verify unexpected requests through official channels never through a callback number provided in an unsolicited message.
Linked Number Security
Your Google Voice number is linked to a forwarding number. If your forwarding number is compromised, calls and texts can be intercepted. Review your linked numbers under Settings → Account and remove any number you did not add personally.
Data Storage and Encryption for Google Voice
Understanding how Google stores and encrypts Voice data helps you make informed decisions about what information remains in your account.
How Google Encrypts Voice Data
Encryption in Transit
All Google Voice communications calls, SMS, and voicemail are encrypted in transit using TLS (Transport Layer Security). This prevents interception of data as it travels between your device and Google’s servers.
Encryption at Rest
Google encrypts stored data at rest across its infrastructure using AES-256 encryption. This applies to your stored call logs, voicemail recordings, and message history.
Data Retention and Deletion
Account-Level Data Deletion
You can delete all Google Voice data by navigating to myaccount.google.com/delete-services and removing Google Voice from your account. This permanently deletes your number, history, and associated data.
Partial Data Cleanup
For regular maintenance, use Google Takeout (takeout.google.com) to export your Voice data before deletion, preserving records locally while clearing them from Google’s servers.
Google Voice and Third-Party Number Providers
If you use Google Voice numbers alongside accounts from providers like Bulk PVA Services, ensure each number operates under its own isolated security profile. Using separate Google Accounts for different number pools with independent 2SV settings prevents a single compromised account from exposing your entire number inventory.
Frequently Asked Questions
1. Can someone hack my Google Voice number?
Yes, through SIM-swapping, phishing, or unauthorized third-party app access. Enabling 2-step verification with an authenticator app and auditing connected apps significantly reduces this risk.
2. Does Google Voice encrypt my calls?
Google Voice encrypts calls in transit using TLS. However, calls between Google Voice and standard PSTN numbers pass through carrier infrastructure where end-to-end encryption is not guaranteed.
3. Can I hide my Google Voice number from recipients?
Google Voice does not offer native caller ID masking. However, you can use a separate Google Voice number as your outward-facing identity to keep your personal number private.
4. How do I stop spam calls on Google Voice?
Enable the spam filter under Settings → Calls, block individual numbers after receiving spam, and avoid publishing your Google Voice number on public directories or websites.
5. What happens to my data if I delete my Google Voice account?
Deleting Google Voice removes your number, call history, voicemails, and messages from Google’s active servers. Residual data may remain in backup systems for a period consistent with Google’s data retention policy.
6. Is Google Voice safe for business use?
Google Voice is suitable for small business use with proper security configuration. For high-volume or multi-user operations, enterprise-grade communication platforms with dedicated compliance features offer stronger data governance.
7. Can third-party apps read my Google Voice messages?
Yes, if you have granted them the appropriate permission scope. Review connected apps at myaccount.google.com/permissions and revoke message-access permissions from apps that do not require them.
8. How do I recover a compromised Google Voice account?
Go to accounts.google.com/signin/recovery, verify your identity through backup codes or recovery email, then immediately revoke all connected app access and change your password.
9. Does Google Voice store voicemail transcripts permanently?
By default, yes. Transcripts remain stored until manually deleted. You can set auto-delete preferences in Google Activity Controls or delete voicemails individually from the app.
10. Can I use Google Voice numbers for account verification on other platforms?
Google Voice numbers are accepted for SMS verification on many platforms, though some services explicitly block VoIP numbers. For platforms requiring phone-verified numbers with higher trust scores, Bulk PVA Services provides dedicated phone-verified accounts built specifically for platform registration and verification workflows.
Protecting Your Number Starts With the Right Account Foundation
Google Voice security is only as strong as the account it is built on. Two-step verification, permission audits, spam filtering, and data controls form the baseline but the quality and verification status of the underlying account matter equally.
For users who need pre-verified, clean-history accounts for Google Voice operations, Bulk PVA Services supplies phone-verified iCloud email accounts that support multi-platform account management with clean IP creation and instant delivery. Every account is manually created and SIM-verified, giving you a stable foundation for secure, isolated number operations.